Keep getting hacked
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Plusnet Community
- :
- Forum
- :
- Help with my Plusnet services
- :
- Fibre Broadband
- :
- Re: Keep getting hacked
Re: Keep getting hacked
14-02-2019 1:31 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
@Anonymous
Taking this off topic is not going to help the OP. I have no doubt that you and your neighbours are on different phases or agree that this is good practice in order to share the load on the local distribution transformer. This doesn't mean that all houses are diligently connected in this way or that due to inter core capacitance the Powerline data can't transfer between phases, be it severely attenuated.
Moderator and Customer
If this helped - select the Thumb
If it fixed it, help others - select 'This Fixed My Problem'
Re: Keep getting hacked
14-02-2019 3:08 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
@wolfheart, OK, the wlx... interface name had me curious, and I had a bit of time spare, so I did some sleuthing..
I downloaded the source code to the Archer firmware (it is GPL open source!), and the wlx... interface name is indeed the Archer's wireless LAN interface (using a Broadcom chipset).
So that appearing in the routing table when the WiFi is enable is perfectly normal (in fact it not appearing would be abnormal).
It would almost certainly disappear if the WiFi was switched off.
The Archer is in fact a very secure router, so as long as a good key is used there is very little chance of anyone hacking in through the WiFi, and it would almost certainly be beyond the capability of any undergraduate student I've ever met (and I have met quite a few).
Even then, if you have the ARP MAC filtering in place, even hacking the WiFi key wouldn't give anyone access to your network, as the router wouldn't allow their device to be routable.
So the one possible weakness looks to be the powerline adapters. Is there any chance of using ethernet cables instead? Or possibly a WiFi repeater to get coverage to where it is required?
Re: Keep getting hacked
14-02-2019 3:10 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
@wolfheart Have you tried using only ethernet cable as suggested already by @Baldrick1?
Re: Keep getting hacked
14-02-2019 6:43 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
Hi,
As far as I am aware their is no way of accessing the power line adaptors apart from with physical access. Their seems to be no i.p or login for them either. I also know I am being hacked as I use linux and windows and the turn my wifi off etc, and as for linux you would need to know what your doing and install a root kit at least. (I have checked for root-kits and none found). but I have over heard my students next door to me, actually say my password for my email and network. I have changed all these and yet they still getting in so I would assume the power line adaptors need to be removed and run ethernet cables directly instead.
I hope to sort this out tonight, I will move everything and also set-up an access point with the old router. I am currently waiting on some other stuff to set up a physical firewall also and a suprise for naughty hackers ![]()
Re: Keep getting hacked
14-02-2019 6:59 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
The issue with powerline adapters is that they use the mains wiring to carry the signal - it is possible for that signal to travel some distance (depending on the noise). It can only carry on the same phase of the mains (as it is only connected to one phase). Typically (but not universally) neighbouring houses are connected to different phases in order to spread the load more or less equally - so typically a house will share a phase with one 3 doors away, but not with the house next door.
It is unlikely, but possible for another powerline adapter to interfere with yours, or even connect to the network. They generally don't have an IP address allocated as they are transparent - they aren't switches, just an interconnection in the same way as an ethernet cable is. Most do have some encryption, but the security of that is variable.
It is the only way I can see that anyone could connect to your network if your WiFi key is secure. Take care with "surprises". They can backfire, or cause you more trouble than the problem they are intended to solve.
Re: Keep getting hacked
14-02-2019 7:08 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
@wolfheart wrote:
Hi,
I keep getting hacked and I believe its number 16, 18 and 9 in my street. Here is evidence and this mac 20e5170c0f3c does not belong to us (they even booted me off my router admin page when I was seeing who was on it). Can you please do something about this? It is getting very annoying and they already broke one power line adaptor ( I believe they are using wireshark to crack the wfi , as wireshark is a well known hacking tool for cracking wifi passwords). I don't believe they have the knowledge of Kali Linux and how to use its tools. I keep changing the router password etc, but they just re-crack it. They have even read my emails so I changed my passwords. I know this as they are uni students with big mouths and I over hear everything they say. I heard them mention my password and other stuff, they have been causing problems since I reported them for there noise, we have had problems with uni students since 2007 (when the college got uni status 2007). I also want to add they are hiding from the router detecting them from being picked up via the admin page, but I can can still scan the network and see who is on it etc. I even have it set so only binded macs are allowed yet they are getting on.
Thank You
Wolfheart
wolfheart@wolfheart-GE60-2QD:~$ route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.0.1 0.0.0.0 UG 0 0 0 wlan0
0.0.0.0 192.168.0.1 0.0.0.0 UG 600 0 0 wlan0
0.0.0.0 192.168.0.1 0.0.0.0 UG 601 0 0 wlx20e5170c0f3c
169.254.0.0 0.0.0.0 255.255.0.0 U 1000 0 0 wlan0
192.168.0.0 0.0.0.0 255.255.255.0 U 0 0 0 wlan0
192.168.0.0 0.0.0.0 255.255.255.0 U 0 0 0 wlx20e5170c0f3c
192.168.0.0 0.0.0.0 255.255.255.0 U 600 0 0 wlan0
192.168.0.0 0.0.0.0 255.255.255.0 U 601 0 0 wlx20e5170c0f3c
192.168.0.1 0.0.0.0 255.255.255.255 UH 0 0 0 wlx20e5170c0f3c
192.168.0.1 0.0.0.0 255.255.255.255 UH 0 0 0 wlan0
192.168.250.0 0.0.0.0 255.255.255.0 U 0 0 0 anbox0
212.227.81.55 192.168.0.1 255.255.255.255 UGH 0 0 0 wlan0
wolfheart@wolfheart-GE60-2QD:~$
I've got an Archer VR400 - which I assume is very similar.
It comes with a guest wifi - which could be enabled, and without a password?
BTW Wireshark is not a hacking tool for cracking passwords - although it will reveal MAC addresses provided that the user has already cracked your WPA2 passwords (you aren't using WEP are you?).
Why is your PC showing all those routes?
"In The Beginning Was The Word, And The Word Was Aardvark."
Re: Keep getting hacked
14-02-2019 7:43 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
@VileReynard, I believe the routing table is from the router, not a PC. The wlx... interface is the Broadcom WiFi interface.
If you have a not-dissimilar router could you check your routing table to confirm to Wolfheart that these entries are normal?
Re: Keep getting hacked
14-02-2019 7:50 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
@VileReynard wrote:
BTW Wireshark is not a hacking tool for cracking passwords - although it will reveal MAC addresses provided that the user has already cracked your WPA2 passwords (you aren't using WEP are you?).
The MAC addresses are always visible without needing to crack or otherwise possess the password.
Re: Keep getting hacked
14-02-2019 8:11 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
I thought that - but the telnet interface is fairly limited
I tried help & got this:-
TP-Link#help
normal mode commands:
clear --- clear screen
exit --- leave to the privious mode
help --- help info
history --- show histroy commands
logout --- logout cli model
config mode commands:
config --- enter config mode
adsl --- config adsl
igmp --- igmp config
wan --- wan config
wlctl --- wireless config
iptv --- iptv config
lan --- lan config
dev --- device control
debug --- debug cmd
Spelling is obviously not a strong point!
I tried a few of the info-style sub-commands, but none relates to routing.
BTW When I bought this router I actually got a tiny printed version of the GPL. ![]()
"In The Beginning Was The Word, And The Word Was Aardvark."
Re: Keep getting hacked
14-02-2019 8:27 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
I downloaded the user guide for the Archer c5400 v2 and that seems pretty comprehensive - perhaps your VR400 is different.
Can you get info from the GUI? i.e. Advanced -> Network -> ?
Re: Keep getting hacked
14-02-2019 8:55 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
Well, there is no routing details, but anything that connected in the last 24 hours gets shown as a recognised device.
The CLI doesn't really show anything extra to the GUI.
Note:- the static routings entry is empty - I presume that's for a bridge mode connection.
"In The Beginning Was The Word, And The Word Was Aardvark."
Re: Keep getting hacked
14-02-2019 9:11 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
Hmm, there seems to be some difference in approach between the two models. One is quite simple and straightforward, and the other is more comprehensive but perhaps harder to understand and easier to misinterpret.
Re: Keep getting hacked
15-02-2019 4:46 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
Hi,
Now I have checked again today and their is one more extra than last time and different name. I also know its the students next door to me as I have heard them talk about my email password etc and even heard them mentioning cracking my network password.
route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.0.1 0.0.0.0 UG 0 0 0 wlp5s0
0.0.0.0 192.168.0.1 0.0.0.0 UG 600 0 0 wlp5s0
169.254.0.0 0.0.0.0 255.255.0.0 U 1000 0 0 anbox0
192.168.0.0 0.0.0.0 255.255.255.0 U 0 0 0 wlp5s0
192.168.0.0 0.0.0.0 255.255.255.0 U 600 0 0 wlp5s0
192.168.0.1 0.0.0.0 255.255.255.255 UH 0 0 0 wlp5s0
192.168.250.0 0.0.0.0 255.255.255.0 U 0 0 0 anbox0
also as you can see below this is the actual connections that belong to me and my brother :-
|
wolfheart-GE60-2QD
|
|
192.168.0.132
|
|
34-E6-AD-55-B0-CC
|
|
Galaxy-S9
|
|
192.168.0.137
|
|
6C-C7-EC-6B-AE-D5
|
|
LGwebOSTV
|
|
192.168.0.130
|
20-3D-BD-FC-E3-EA
the ones above are all mine (wireless) and this one below is my brothers (wired via power line adaptor).
|
WORKGROUP
|
|
192.168.0.163
|
60-45-CB-A0-DC-E7
So as you can see it them other 4 and 5 today do not belong to us.
Re: Keep getting hacked
15-02-2019 5:11 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
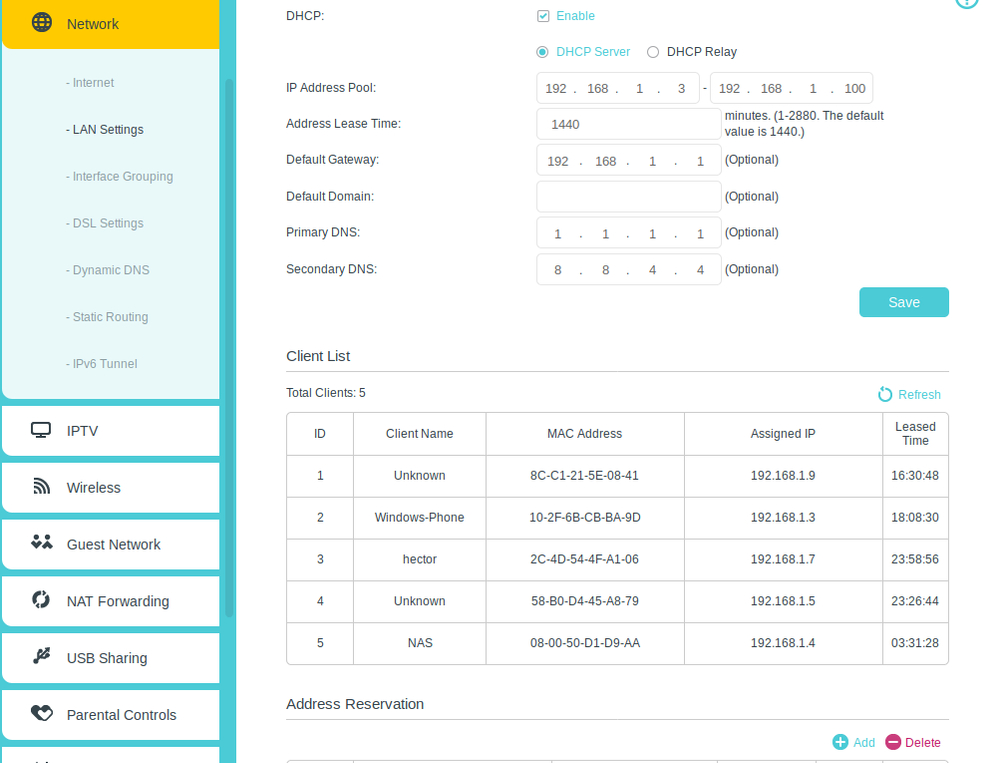
Could you instead go into the GUI interface where it shows connected devices, ip addresses & MAC addresses.
Take a screenshot of the relevant area (like I did).
That way we don't need to untangle internal router bits.
Note that this router retains addresses of devices that have been allocated addresses by DHCP in the last 24 hours (typically).
I've noticed that mobiles seem to get allocated fresh ip addresses if they get contacted several times in one day.
Why are these people able to break long WPA2 passwords so easily?
Try getting a new password from https://passwordsgenerator.net/ - this way avoids guessable passwords.
Use a long password - say 10-12 characters including special characters.
"In The Beginning Was The Word, And The Word Was Aardvark."
Re: Keep getting hacked
15-02-2019 6:27 PM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Highlight
- Report to Moderator
@VileReynard wrote:
Why are these people able to break long WPA2 passwords so easily?
Perhaps the router's WiFi has WPS enabled, as that dramatically shortens the time needed to hack WPA2.
Would I be right in assuming that the email password being hacked is for Plusnet email ?
If so it would be worth using a different email provider that supports TLS encyrption, rather than the useless Plusnet plain text password that can be read by anyone with a WiFi adaptor that features monitor mode.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Plusnet Community
- :
- Forum
- :
- Help with my Plusnet services
- :
- Fibre Broadband
- :
- Re: Keep getting hacked